Android Apk Upload Failed Signed With Different Certificate
Android requires that all APKs exist digitally signed with a document before they are installed on a device or updated. When releasing using Android App Bundles, you need to sign your app bundle with an upload key earlier uploading information technology to the Play Panel, and Play App Signing takes care of the rest. For apps distributing using APKs on the Play Store (created earlier August 2021) or on other stores, you must manually sign your APKs for upload.
This folio guides you through some important concepts related to app signing and security, how to sign your app for release to Google Play using Android Studio, and how to configure Play App Signing.
The post-obit is a high-level overview of the steps you might need to have to sign and publish a new app to Google Play:
- Generate an upload key and keystore
- Sign your app with your upload fundamental
- Configure Play App Signing
- Upload your app to Google Play
- Prepare & ringlet out release of your app
If instead your app is already published to the Google Play Store with an existing app signing fundamental, or you would like to choose the app signing key for a new app instead of having Google generate it, follow these steps:
- Sign your app with your app'south signing cardinal and select the option to encrypt and export its signing key.
- Upload your app's signing cardinal to Play App Signing.
- (Recommended) Generate and register an upload certificate for future updates to your app
- Upload your app to Google Play
- Prepare & gyre out release of your app
This page also explores how to manage your own keys for when uploading your app to other app stores. If y'all practice non use Android Studio or would rather sign your app from the command line, learn nigh how to utilise apksigner.
Play App Signing
With Play App Signing, Google manages and protects your app's signing key for you lot and uses it to sign your APKs for distribution. And, considering app bundles defer building and signing APKs to the Google Play Store, y'all need to configure Play App Signing before you lot upload your app parcel. Doing and so lets you benefit from the post-obit:
- Apply the Android App Parcel and back up Google Play's advanced commitment modes. The Android App Parcel makes your app much smaller, your releases simpler, and makes information technology possible to use characteristic modules and offering instant experiences.
- Increase the security of your signing key, and go far possible to use a separate upload key to sign the app packet you upload to Google Play.
-
One time key upgrade for new installs lets yous change your app signing key in case your existing one is compromised or if you need to migrate to a cryptographically stronger fundamental
Play App Signing uses 2 keys: the app signing fundamental and the upload key, which are described in further detail in the section about Keys and keystores. Y'all continue the upload fundamental and use it to sign your app for upload to the Google Play Shop. Google uses the upload document to verify your identity, and signs your APK(south) with your app signing key for distribution every bit shown in figure 1. By using a separate upload key you can request an upload key reset if your central is ever lost or compromised.
By comparison, for apps created earlier August 2021 that accept not opted in to Play App Signing, if y'all lose your app'southward signing key, you lose the power to update your app.
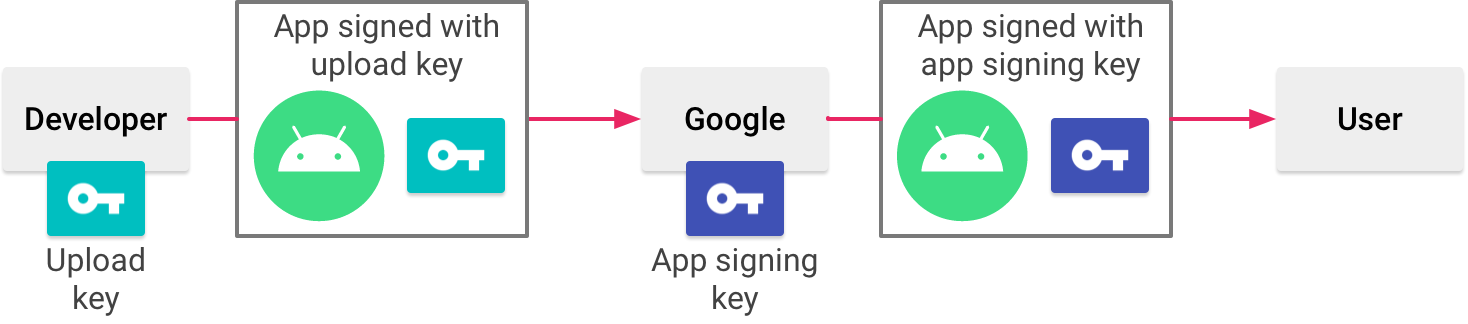
Figure 1. Signing an app with Play App Signing
Your keys are stored on the same infrastructure that Google uses to store its own keys, where they are protected by Google's Fundamental Management Service. You can learn more than almost Google'due south technical infrastructure by reading the Google Cloud Security Whitepapers.
When you employ Play App Signing, if you lose your upload key, or if it is compromised, yous tin can contact Google to revoke your old upload central and generate a new ane. Considering your app signing key is secured by Google, you tin proceed to upload new versions of your app as updates to the original app, even if you change upload keys. To larn more, read Reset a lost or compromised private upload key.
The next section describes some of import terms and concepts related to app signing and security. If you lot'd rather skip ahead and learn how to prepare your app for upload to the Google Play Shop, go to Sign your app for release.
Keystores, keys, and certificates
Coffee Keystores (.jks or .keystore) are binary files that serve as repositories of certificates and private keys.
A public key certificate (.der or .pem files), also known every bit a digital certificate or an identity certificate, contains the public primal of a public/private key pair, as well as some other metadata identifying the possessor (for example, proper name and location) who holds the corresponding private fundamental.
The post-obit are the dissimilar types of keys you should understand:
- App signing central: The key that is used to sign APKs that are installed on a user'south device. As office of Android'due south secure update model, the signing fundamental never changes during the lifetime of your app. The app signing key is private and must be kept secret. You can, nevertheless, share the certificate that is generated using your app signing primal.
-
Upload fundamental: The fundamental you apply to sign the app package or APK earlier y'all upload it for app signing with Google Play. You must keep the upload fundamental undercover. However, you tin can share the certificate that is generated using your upload key. Y'all may generate an upload key in one of the post-obit ways:
- If you choose for Google to generate the app signing fundamental for y'all when you opt in, so the key you lot use to sign your app for release is designated as your upload key.
- If you provide the app signing key to Google when opting in your new or existing app, then yous have the pick to generate a new upload fundamental during or after opting in for increased security.
- If y'all practice non generate a new upload primal, you continue to utilise your app signing key equally your upload key to sign each release.
Tip: To continue your keys secure, it's a skillful idea to make certain your app signing primal and upload primal are different.
Working with API providers
Yous can download the document for the app signing primal and your upload key from the Release > Setup > App Integrity page in the Play Panel. This is used to register public key(south) with API providers; it'south intended to be shared, as it does non contain your private cardinal.
A certificate fingerprint is a short and unique representation of a certificate that is often requested by API providers alongside the package proper name to annals an app to employ their service. The MD5, SHA-ane and SHA-256 fingerprints of the upload and app signing certificates can be found on the app signing page of the Play Panel. Other fingerprints can too be computed by downloading the original document (.der) from the same folio.
Sign your debug build
When running or debugging your project from the IDE, Android Studio automatically signs your app with a debug certificate generated by the Android SDK tools. The offset time you run or debug your projection in Android Studio, the IDE automatically creates the debug keystore and document in $Domicile/.android/debug.keystore, and sets the keystore and primal passwords.
Because the debug document is created past the build tools and is insecure by blueprint, nearly app stores (including the Google Play Shop) do not accept apps signed with a debug certificate for publishing.
Android Studio automatically stores your debug signing data in a signing configuration and so you exercise not accept to enter it every time yous debug. A signing configuration is an object consisting of all of the necessary information to sign your app, including the keystore location, keystore password, key name, and key password.
For more information well-nigh how to build and run apps for debugging, encounter Build and Run Your App.
Expiry of the debug certificate
The self-signed certificate used to sign your app for debugging has an expiration date of 30 years from its creation engagement. When the certificate expires, you get a build fault.
To set this problem, simply delete the debug.keystore file stored in one of the following locations:
-
~/.android/on Os 10 and Linux -
C:\Documents and Settings\user\.android\on Windows XP -
C:\Users\user\.android\on Windows Vista and Windows 7, 8, and ten
The next time yous build and run a debug version of your app, Android Studio regenerates a new keystore and debug key.
Sign your app for release to Google Play
When you are gear up to publish your app, you need to sign your app and upload information technology to an app shop, such as Google Play. When publishing your app to Google Play for the showtime time, yous must also configure Play App Signing. Play App Signing is optional for apps created earlier August 2021. This section shows you how to properly sign your app for release and configure Play App Signing.
Generate an upload central and keystore
If you don't already take an upload cardinal, which is useful when configuring Play App Signing, you tin generate 1 using Android Studio as follows:
- In the menu bar, click Build > Generate Signed Bundle/APK.
- In the Generate Signed Bundle or APK dialog, select Android App Parcel or APK and click Next.
- Below the field for Key shop path, click Create new.
-
On the New Cardinal Store window, provide the following information for your keystore and cardinal, equally shown in figure 2.
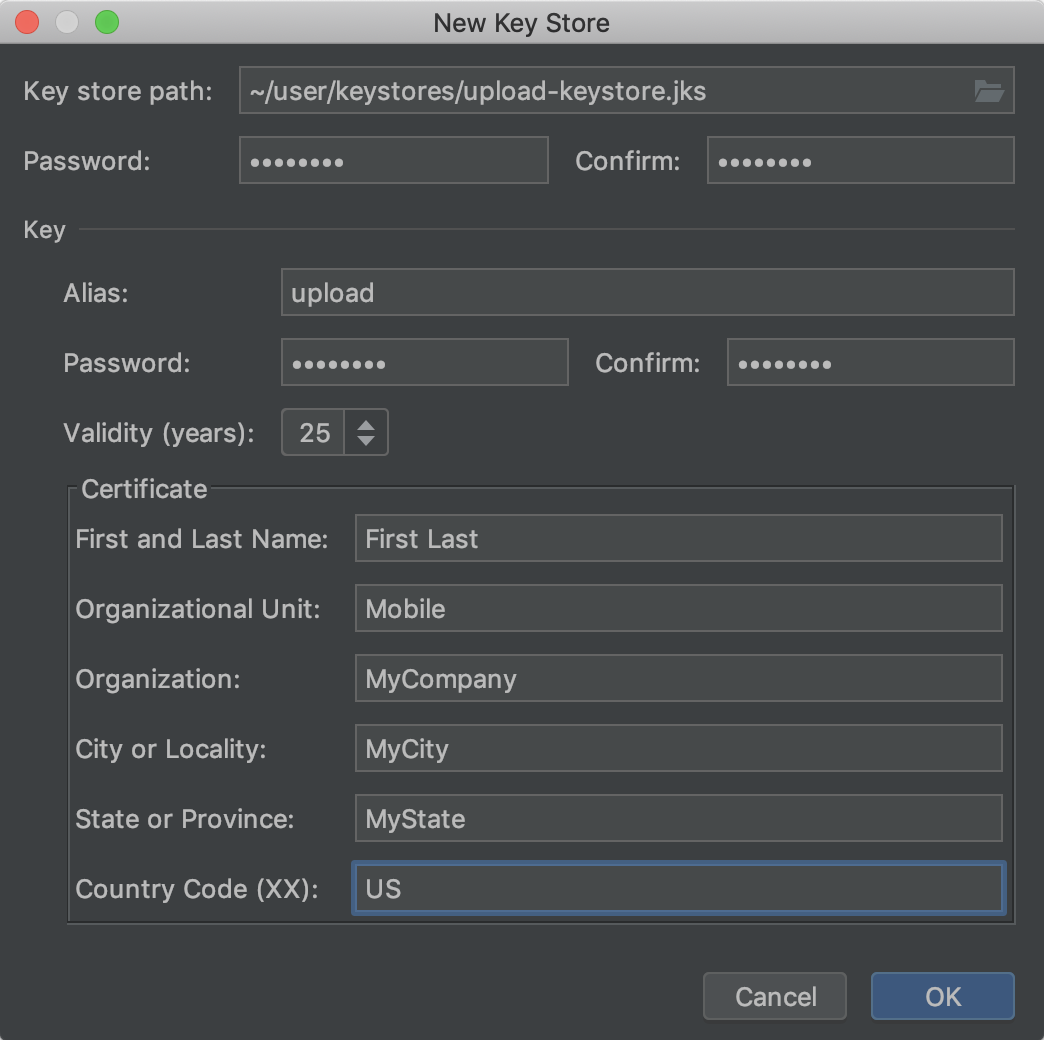
Figure 2. Create a new upload key and keystore in Android Studio.
-
Keystore
- Fundamental store path: Select the location where your keystore should be created. Besides, a file name should exist added to the end of the location path with the
.jksextension. - Password: Create and ostend a secure password for your keystore.
- Fundamental store path: Select the location where your keystore should be created. Besides, a file name should exist added to the end of the location path with the
-
Cardinal
- Alias: Enter an identifying name for your key.
- Password: Create and ostend a secure countersign for your key. This should exist the same as your keystore countersign. (Please refer to the known outcome for more information)
- Validity (years): Ready the length of fourth dimension in years that your key will be valid. Your key should be valid for at to the lowest degree 25 years, so you can sign app updates with the same key through the lifespan of your app.
- Certificate: Enter some information about yourself for your certificate. This data is non displayed in your app, but is included in your certificate equally function of the APK.
-
Once you consummate the class, click OK.
-
If you lot would similar to build and sign your app with your upload primal, keep to the department nigh how to Sign your app with your upload fundamental. If you only want to generate the cardinal and keystore, click Abolish.
Sign your app with your central
If you lot already have an upload key, use information technology to sign your app. If instead your app is already signed and published to the Google Play store with an existing app signing key, use it to sign your app and brand certain to encrypt and export it to opt your app in to Play App Signing. You can later generate a split upload cardinal and annals your upload key's public certificate with Google Play to sign and upload subsequent updates to your app.
To sign your app using Android Studio, and export an existing app signing key, follow these steps:
- If you don't currently have the Generate Signed Bundle or APK dialog open up, click Build > Generate Signed Package/APK.
- In the Generate Signed Bundle or APK dialog, select either Android App Packet or APK and click Next.
- Select a module from the drop down.
-
Specify the path to your keystore, the alias for your cardinal, and enter the passwords for both. If you haven't notwithstanding prepared your upload keystore and key, first Generate an upload key and keystore and so render to consummate this step.
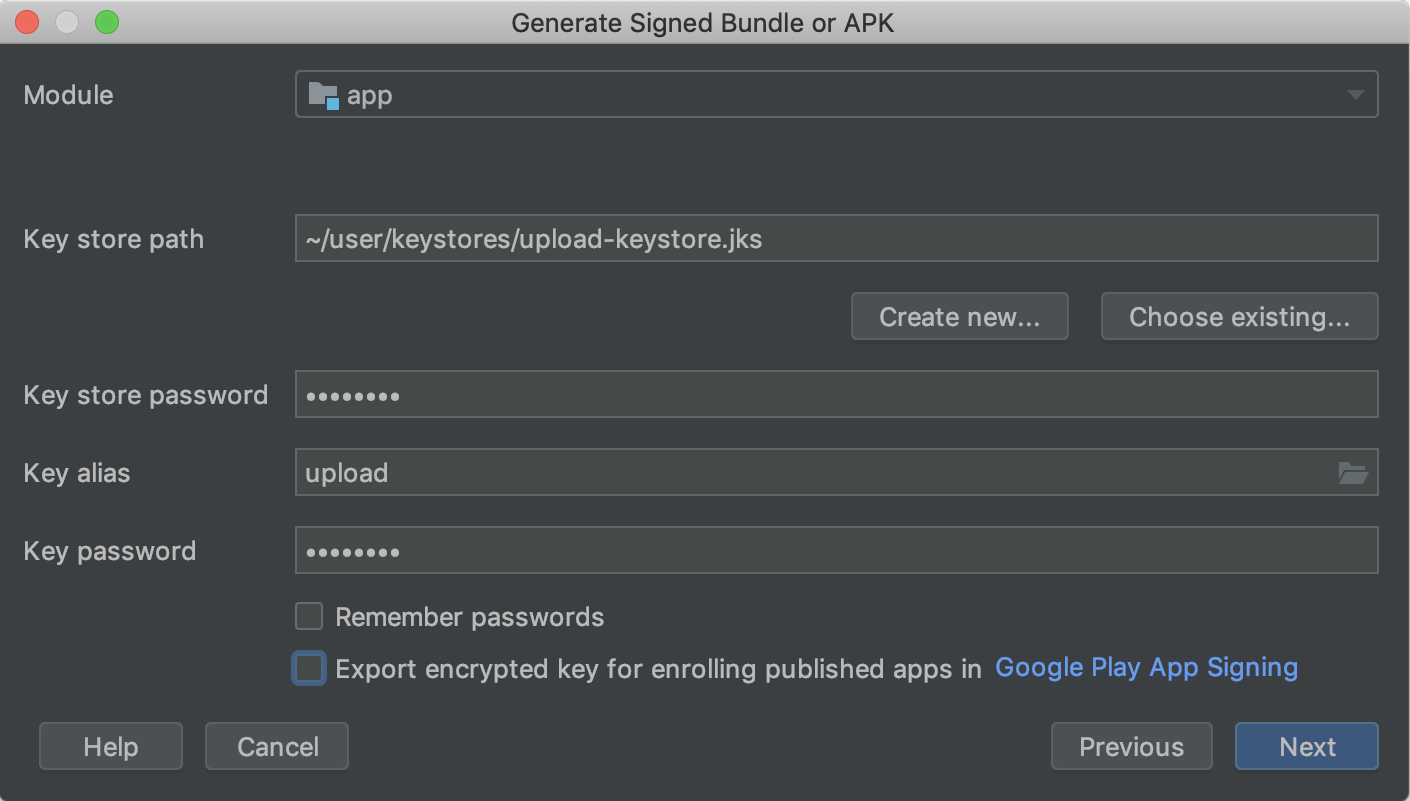
Figure 3. Sign your app with your upload cardinal.
-
If you're signing an app package with an existing app signing key, and you'd like to later opt your app in to Play App Signing, check the box side by side to Consign encrypted key and specify a path to salve your signing key as an encrypted
*.pepkfile. Y'all tin then use your encrypted app signing key to opt in an existing app into Play App Signing. -
Click Next.
-
In the adjacent window (shown in figure 4), select a destination folder for your signed app, select the build type, choose the production flavour(s) if applicative.
-
If you are edifice and signing an APK, you need to select which Signature Versions you want your app to support. To learn more than, read about app signing schemes
-
Click Cease.
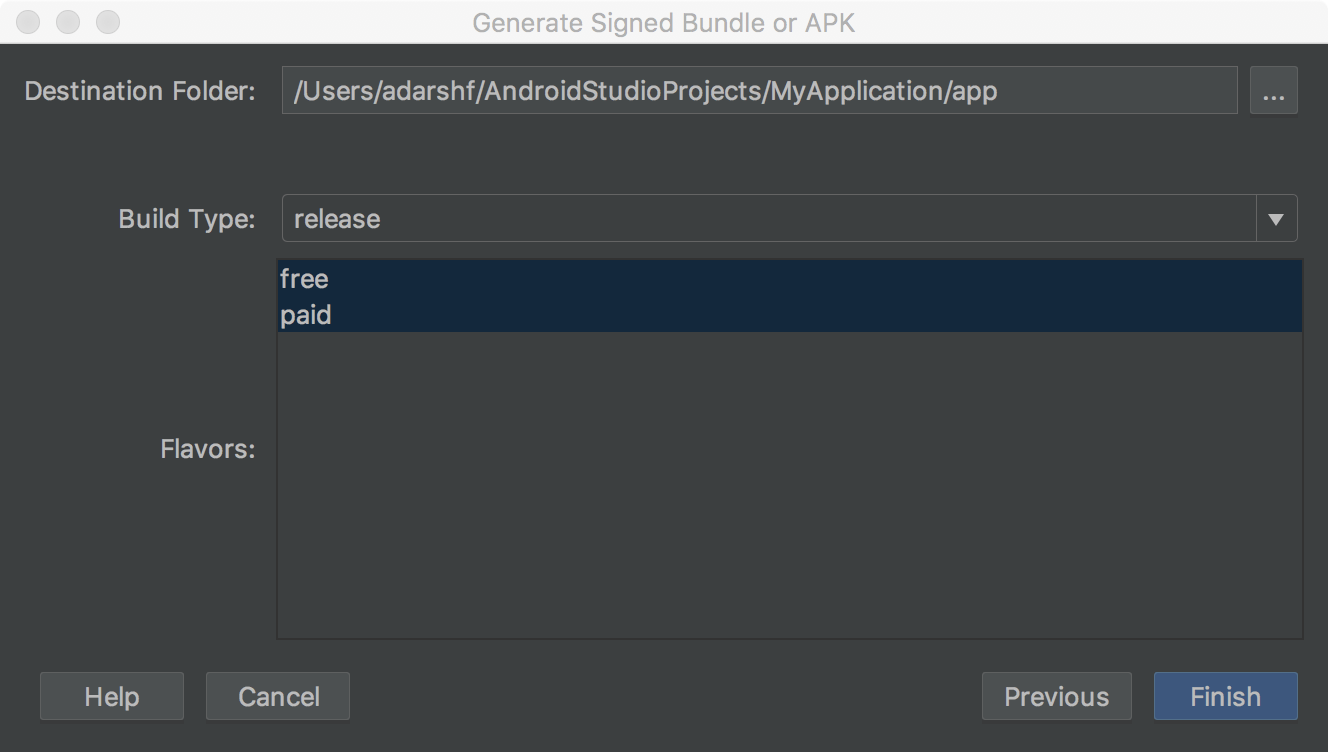
Effigy 4. Generate a signed version of your app for the selected product flavors.
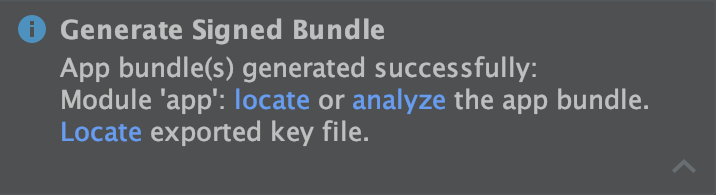
Figure 5. Click the link in the popup to clarify or locate your app bundle, or locate your exported signing cardinal.
After Android Studio finishes building your signed app, yous tin can either locate or analyze your app by clicking on the appropriate option in the pop-up notification. If you selected the option to export your signing key, you can speedily navigate to information technology past clicking the dropdown arrow in the bottom right corner of the popup to aggrandize it and clicking Bear witness Exported Key File, as shown in figure v.
Now you're gear up to opt your app in to Play App Signing and upload your app for release. If you're new to the app publishing process, you may want to read the Launch overview. Otherwise, continue to the page about how to Upload your app to the Play Panel.
Using Play App Signing
As described earlier in this page, configuring Play App Signing is required to sign your app for distribution through Google Play (except for apps created before August 2021, which may continue distributing self-signed APKs). The steps you lot need to have depend on whether your app has non nonetheless been published to Google Play, or your app is already signed and was published before August 2021 using an existing app signing key.
Configure a new app
To configure signing for an app that has non yet been published to Google Play, keep as follows:
- If you lot haven't already done so, generate an upload key and sign your app with that upload key.
- Sign in to your Play Console.
- Follow the steps to set & roll out your release to create a new release.
- Later yous cull a release runway, configure app signing under the App Integrity section as follows:
- To take Google Play generate an app signing central for you and apply it to sign your app, you don't have to exercise anything. The central you lot use to sign your kickoff release becomes your upload key, and you lot should apply it to sign future releases.
- To utilize the same key equally some other app on your developer account, select Change app signing key > Use my own cardinal > Use the same key as some other app in this business relationship, select an app, and then click Continue.
- To provide your own signing key for Google to use when signing your app, select Change app signing central > Use my ain primal and select i of the options that lets yous securely upload a private key and its public document.
In the section called App Bundles, click Browse files to locate and upload the app you signed using your upload primal. For more information about releasing your app, refer to prepare & scroll out your release. When you release your app later on configuring Play App Signing, Google Play generates (unless you upload an existing key) and manages your app's signing central for you. Simply sign subsequent updates to your app using your app'southward upload cardinal before uploading it to Google Play.
If you need to create a new upload key for you app, go to the section nigh how to Reset a lost or compromised individual upload cardinal.
Opt in an existing app
If you lot're updating an app that's already published to Google Play using an existing app signing key, you can opt in to Play App Signing every bit follows:
- If you haven't already washed so, sign your app using Android Studio with your existing app signing key and make sure to bank check the box next to Export encrypted primal to save your signing primal as an encrypted
*.pepkfile. You'll need this file in a afterward step. This tin can as well be done using the PEPK tool, which you can download from the Play Console. - Sign in to your Play Console and navigate to your app.
- On the left menu, click Release > Setup > App integrity.
- If applicable, review the Terms of Service and select Have.
- Select one of the options that best describes the signing central you desire to upload to Google Play and follow the instructions that are shown. For case, if you used Android Studio to export your app'south signing key, as described on this folio, select Upload a cardinal exported from Android Studio and upload the
*.pepkfile for your central. - Click Enroll.
You should now see a page with the details of your app's signing and upload certificates. Google Play at present signs your app with your existing central when deploying it to users. Nevertheless, ane of the about important benefits to Play App Signing is the ability to separate the primal you apply to sign the artifact you upload to Google Play from the central that Google Play uses to sign your app for distribution to users. So, consider following the steps in the next section to generate and register a separate upload key.
Generate and register an upload certificate
When y'all're publishing an app that is not signed by an upload key, the Google Play Console provides the option to annals one for future updates to the app. Although this is an optional pace, it's recommended that you publish your app with a key that's split from the 1 Google Play uses to distribute your app to users. That way, Google keeps your signing central secure, and you have the option to reset a lost or compromised individual upload key. This section describes how to create an upload fundamental, generate an upload document from it, and register that certificate with Google Play for future updates of your app.
The following describes the situations in which you lot see the selection to register an upload certificate in the Play Console:
- When you publish a new app that'south signed with a signing key and opt information technology in to Play App Signing.
- When you are about to publish an existing app that'southward already opted in to Play App Signing, simply it is signed using its signing key.
If y'all are not publishing an update to an existing app that's already opted in to Play App Signing, and you'd similar to register an upload document, complete the steps below and continue on to the section nearly how to reset a lost or compromised private upload fundamental.
If y'all haven't already washed so, generate an upload key and keystore.
After you create your upload key and keystore, y'all demand to generate a public certificate from your upload primal using keytool, with the following command:
$ keytool -export -rfc -keystore your-upload-keystore.jks -allonym upload-alias -file output_upload_certificate.pem
Now that you have your upload certificate, annals it with Google when prompted in the Play Console or read the department below to annals it though the Google Play support team.
Upgrade your app signing primal
In some circumstances, you might desire to change your app's signing key. For example, because you want a cryptographically stronger key or your signing key has been compromised. All the same, considering users can only update your app if the update is signed with the same signing key, it's difficult to change the signing key for an app that's already published.
If you publish your app to Google Play, you tin can upgrade the signing key for your published app through the Play Console—your new key is used to sign new installs and app updates, while your older app signing central is used to sign updates for users who installed your app before the key upgrade.
To learn more, read Upgrade your app signing key for new installs.
Reset a lost or compromised individual upload cardinal
If yous lost your individual upload key or your private key has been compromised, yous tin can create a new one and contact the Google Play support team to reset the key.
Configure the build process to automatically sign your app
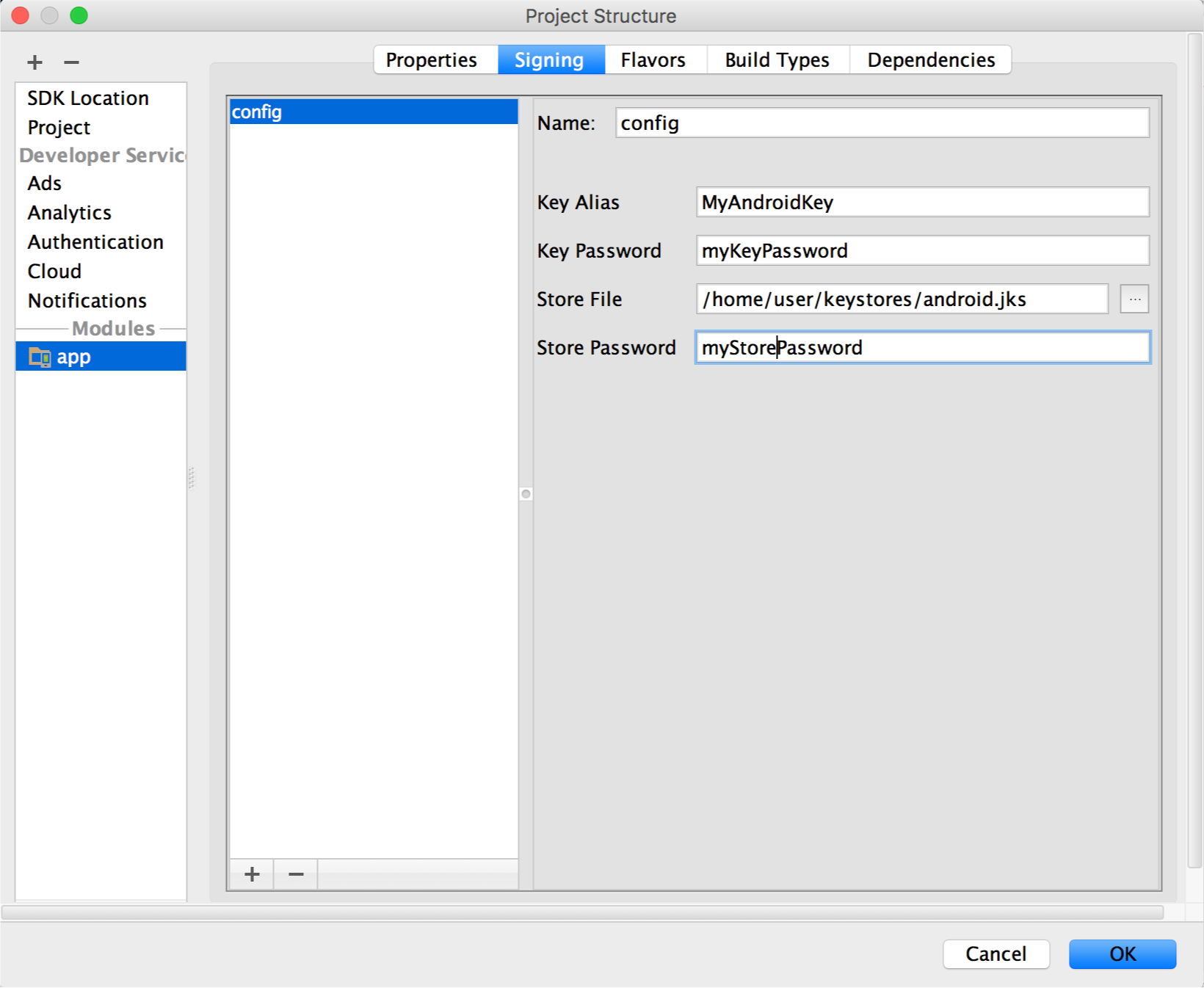
In Android Studio, y'all tin can configure your project to sign the release version of your app automatically during the build process past creating a signing configuration and assigning it to your release build blazon. A signing configuration consists of a keystore location, keystore password, key allonym, and key password. To create a signing configuration and assign it to your release build blazon using Android Studio, complete the following steps:
- In the Project window, correct click on your app and click Open Module Settings.
- On the Project Structure window, nether Modules in the left panel, click the module you lot would like to sign.
- Click the Signing tab, then click Add
 .
. -
Select your keystore file, enter a name for this signing configuration (as you may create more than than one), and enter the required information.
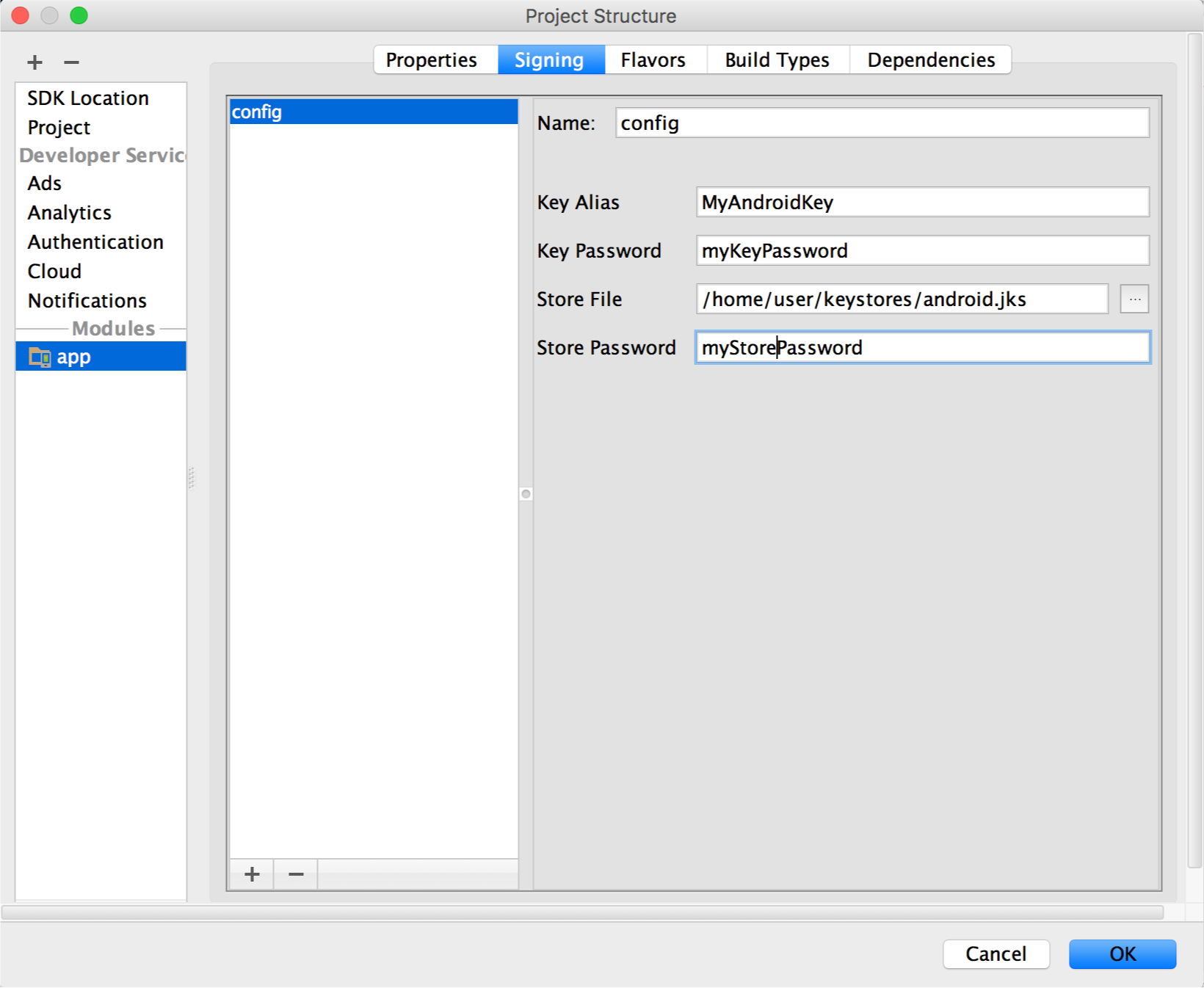
Effigy vii. The window for creating a new signing configuration.
- Click the Build Types tab.
- Click the release build.
-
Under Signing Config, select the signing configuration you just created.
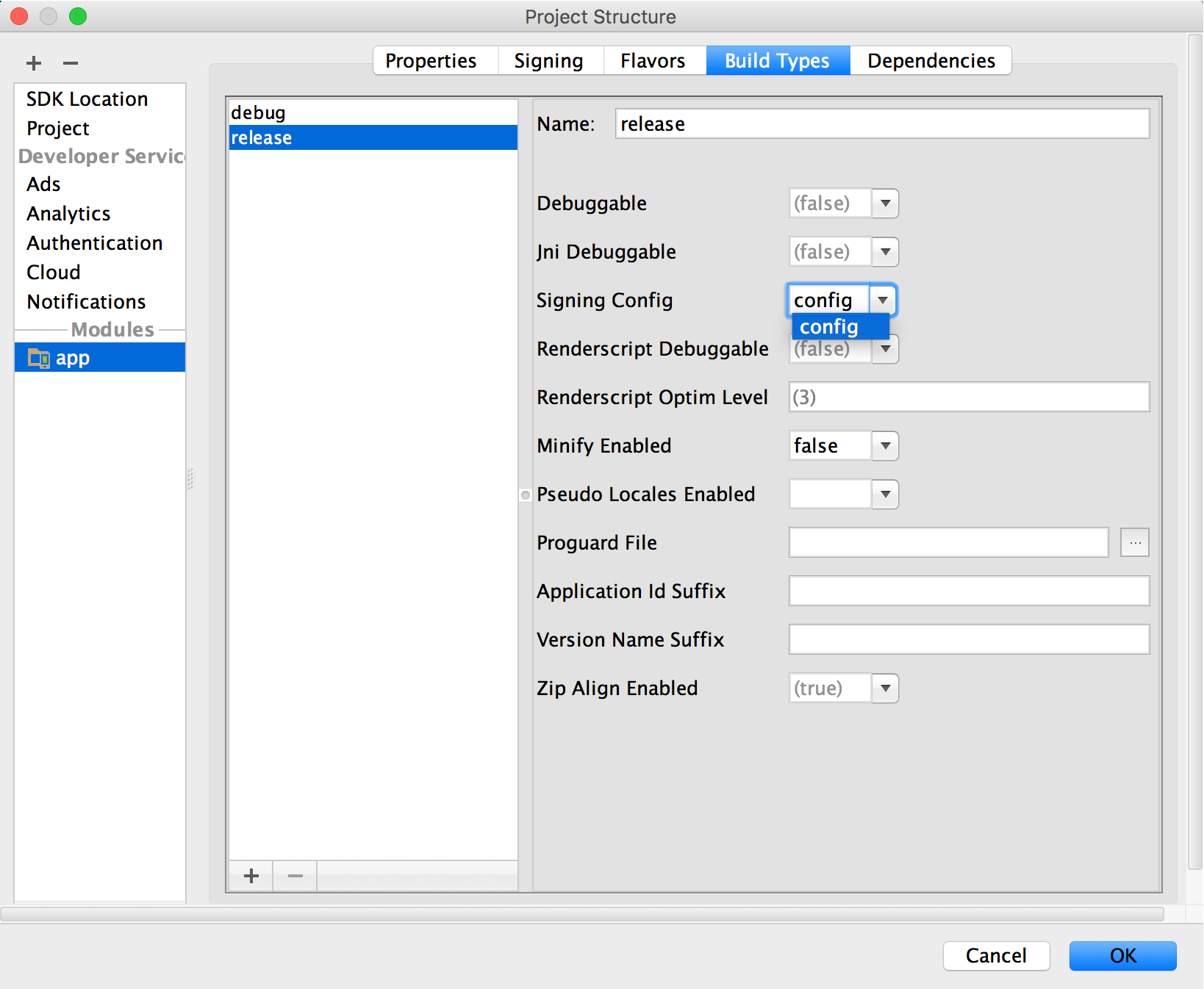
Figure 8. Select a signing configuration in Android Studio.
- Click OK.
Now every time you lot build your release build type by selecting an choice nether Build > Build Parcel(s) / APK(s) in Android Studio, the IDE will sign your app automatically, using the signing configuration you specified. Y'all can find your signed APK or app bundle in the build/outputs/ directory inside the project directory for the module you are building.
When y'all create a signing configuration, your signing information is included in plain text in your Gradle build files. If you lot are working in a team or sharing your lawmaking publicly, you should go along your signing information secure by removing it from the build files and storing it separately. You can read more nearly how to remove your signing information from your build files in Remove Signing Information from Your Build Files. For more about keeping your signing data secure, read Secure your key.
Sign each product flavor differently
If your app uses product flavors and yous would similar to sign each season differently, you can create additional signing configurations and assign them by flavor:
- In the Project window, right click on your app and click Open Module Settings.
- On the Projection Construction window, nether Modules in the left panel, click the module you would like to sign.
- Click the Signing tab, and so click Add together
 .
. -
Select your keystore file, enter a name for this signing configuration (as you may create more than than i), and enter the required information.
Effigy 10. The window for creating a new signing configuration.
- Repeat steps 3 and 4 as necessary until you accept created all your signing configurations.
- Click the Flavors tab.
- Click the flavor you would like to configure, so select the advisable signing configuration from the Signing Config dropdown card.
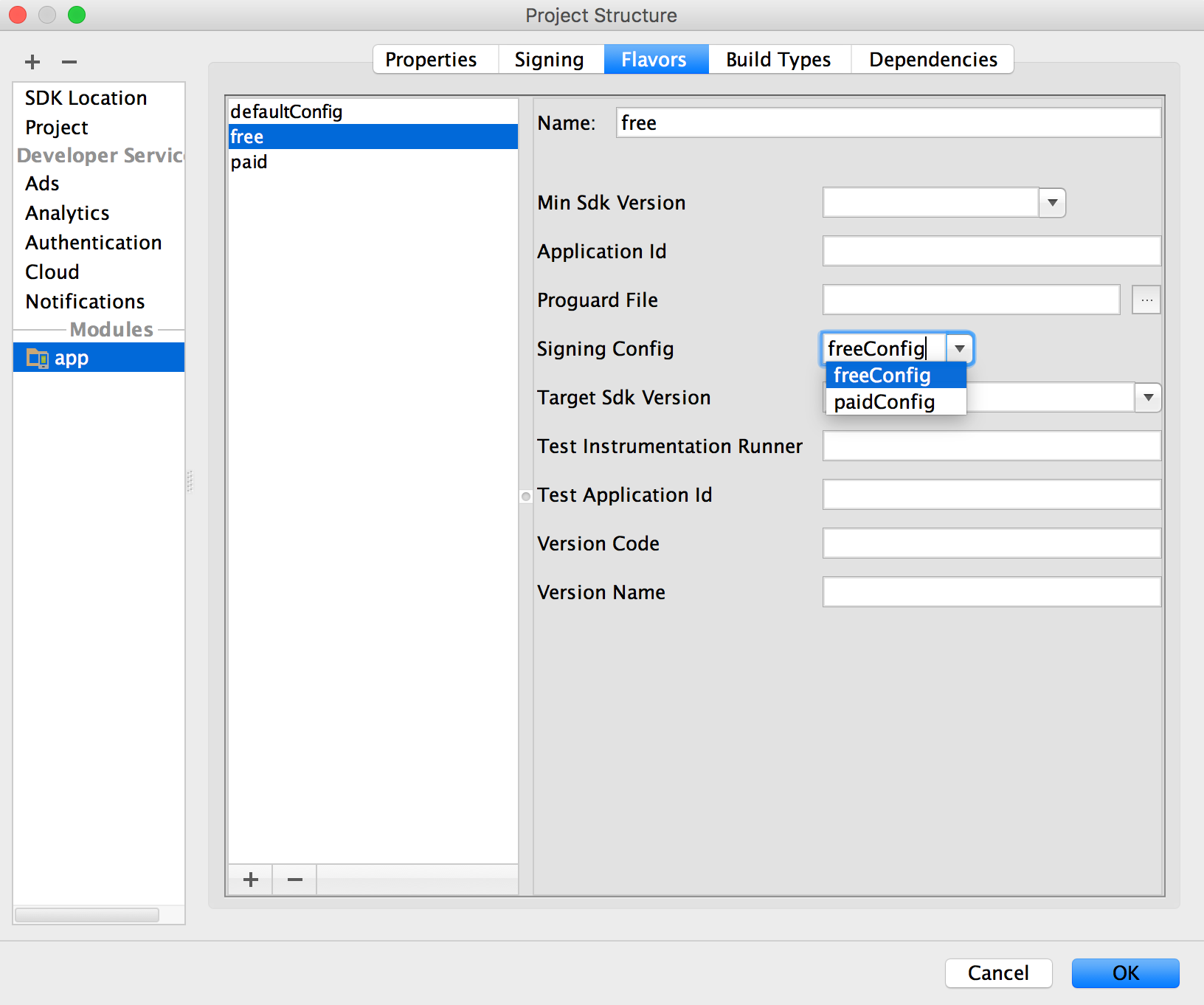
Effigy xi. Configure signing settings by production flavor.
Echo to configure any additional product flavors.
- Click OK.
Y'all can as well specify your signing settings in Gradle configuration files. For more information, run across Configuring Signing Settings.
Manage your own signing key
If you cull non to opt in to Play App Signing (simply for apps created before August 2021), you can manage your ain app signing key and keystore. Go along in heed, you lot are responsible for securing the key and the keystore. Additionally, your app volition non be able to support Android App Bundles, Play Characteristic Delivery and Play Asset Delivery.
When you are ready to create your own key and keystore, brand sure you showtime cull a strong password for your keystore and a carve up strong countersign for each private fundamental stored in the keystore. You must keep your keystore in a condom and secure identify. If you lose access to your app signing fundamental or your central is compromised, Google cannot recall the app signing key for you, and you will non exist able to release new versions of your app to users as updates to the original app. For more information, meet Secure your cardinal, beneath.
If you manage your own app signing fundamental and keystore, when yous sign your APK, y'all volition sign it locally using your app signing cardinal and upload the signed APK straight to the Google Play Shop for distribution every bit shown in effigy 10.
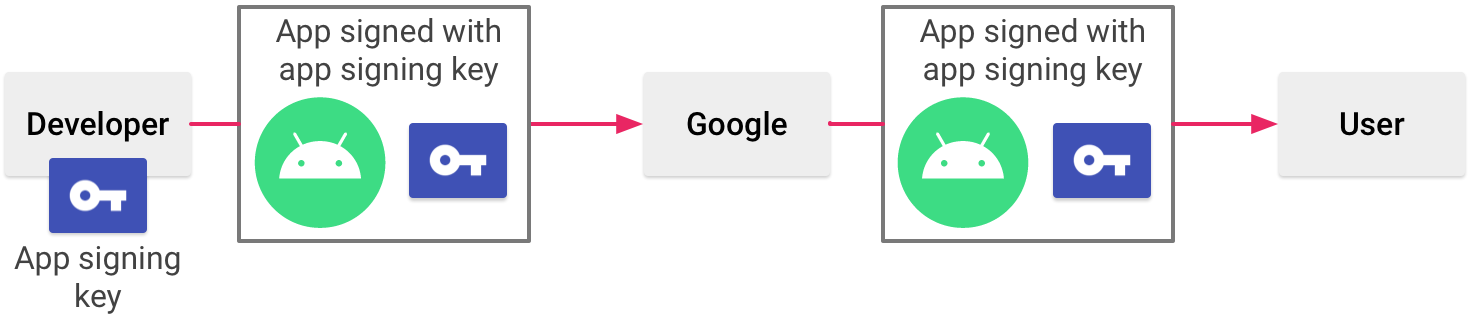
Figure 12. Signing an app when you manage your own app signing key
When you use Play App Signing, Google keeps your signing key safe, and ensures your apps are correctly signed and able to receive updates throughout their lifespans. However, if yous decide to manage your app signing key yourself, in that location are a few considerations y'all should proceed in mind.
Signing considerations
You should sign your app with the same document throughout its expected lifespan. There are several reasons why you should practice and so:
- App upgrade: When the system is installing an update to an app, it compares the certificate(s) in the new version with those in the existing version. The system allows the update if the certificates match. If you lot sign the new version with a different document, you must assign a different packet name to the app—in this case, the user installs the new version as a completely new app.
- App modularity: Android allows APKs signed past the aforementioned document to run in the same process, if the apps so request, and then that the organization treats them as a single app. In this fashion you tin can deploy your app in modules, and users tin update each of the modules independently.
- Code/information sharing through permissions: Android provides signature-based permissions enforcement, so that an app can betrayal functionality to another app that is signed with a specified document. By signing multiple APKs with the same certificate and using signature-based permissions checks, your apps tin can share code and data in a secure manner.
If you plan to support upgrades for an app, ensure that your app signing primal has a validity period that exceeds the expected lifespan of that app. A validity menses of 25 years or more is recommended. When your key'south validity flow expires, users volition no longer exist able to seamlessly upgrade to new versions of your app.
If you plan to publish your apps on Google Play, the fundamental you use to sign your app must have a validity period ending after 22 Oct 2033. Google Play enforces this requirement to ensure that users tin seamlessly upgrade apps when new versions are available.
Keep your key secure
If you lot choose to manage and secure your app signing key and keystore yourself (instead of opting in to Play App Signing), securing your app signing fundamental is of critical importance, both to y'all and to the user. If you let someone to employ your cardinal, or if you leave your keystore and passwords in an unsecured location such that a third-party could find and use them, your authoring identity and the trust of the user are compromised.
If a tertiary party should manage to take your app signing key without your knowledge or permission, that person could sign and distribute apps that maliciously replace your authentic apps or corrupt them. Such a person could also sign and distribute apps under your identity that assail other apps or the organisation itself, or decadent or steal user data.
Your private key is required for signing all futurity versions of your app. If you lose or misplace your primal, you volition not be able to publish updates to your existing app. You lot cannot regenerate a previously generated key.
Your reputation equally a developer entity depends on your securing your app signing key properly, at all times, until the key is expired. Here are some tips for keeping your key secure:
- Select strong passwords for the keystore and fundamental.
- Practice not give or lend anyone your private key, and do not allow unauthorized persons know your keystore and fundamental passwords.
- Keep the keystore file containing your private key in a safe, secure identify.
In general, if you follow common-sense precautions when generating, using, and storing your primal, it will remain secure.
Remove signing information from your build files
When you create a signing configuration, Android Studio adds your signing information in plain text to the module's build.gradle files. If you lot are working with a team or open-sourcing your code, y'all should move this sensitive information out of the build files so it is not easily accessible to others. To do this, you should create a separate properties file to store secure information and refer to that file in your build files equally follows:
- Create a signing configuration, and assign information technology to 1 or more build types. These instructions assume you have configured a single signing configuration for your release build blazon, as described in Configure the build process to automatically sign your app, above.
- Create a file named
keystore.backdropin the root directory of your project. This file should incorporate your signing information, as follows:storePassword=myStorePassword keyPassword=mykeyPassword keyAlias=myKeyAlias storeFile=myStoreFileLocation
- In your module'due south
build.gradlefile, add code to load yourkeystore.propertiesfile before theandroid {}block.Groovy
... // Create a variable called keystorePropertiesFile, and initialize it to your // keystore.backdrop file, in the rootProject binder. def keystorePropertiesFile = rootProject.file("keystore.properties") // Initialize a new Backdrop() object called keystoreProperties. def keystoreProperties = new Properties() // Load your keystore.backdrop file into the keystoreProperties object. keystoreProperties.load(new FileInputStream(keystorePropertiesFile)) android { ... }Kotlin
... import java.util.Properties import coffee.io.FileInputStream // Create a variable called keystorePropertiesFile, and initialize information technology to your // keystore.properties file, in the rootProject folder. val keystorePropertiesFile = rootProject.file("keystore.properties") // Initialize a new Backdrop() object called keystoreProperties. val keystoreProperties = Properties() // Load your keystore.properties file into the keystoreProperties object. keystoreProperties.load(FileInputStream(keystorePropertiesFile)) android { ... }Note: You could cull to store your
keystore.propertiesfile in some other location (for example, in the module folder rather than the root binder for the project, or on your build server if you are using a continuous integration tool). In that instance, you should change the code above to correctly initializekeystorePropertiesFileusing your actualkeystore.propertiesfile's location. - You lot can refer to properties stored in
keystorePropertiesusing the syntaxkeystoreProperties['propertyName']. Modify thesigningConfigsblock of your module'sbuild.gradlefile to reference the signing information stored inkeystorePropertiesusing this syntax.Groovy
android { signingConfigs { config { keyAlias keystoreProperties['keyAlias'] keyPassword keystoreProperties['keyPassword'] storeFile file(keystoreProperties['storeFile']) storePassword keystoreProperties['storePassword'] } } ... }Kotlin
android { signingConfigs { getByName("config") { keyAlias = keystoreProperties["keyAlias"] keyPassword = keystoreProperties["keyPassword"] storeFile = file(keystoreProperties["storeFile"]) storePassword = keystoreProperties["storePassword"] } } ... } - Open the Build Variants tool window and ensure that the release build type is selected.
- Select an option under Build > Build Bundle(s) / APK(s) to build either an APK or app bundle of your release build. Yous should come across the build output in the
build/outputs/directory for your module.
Because your build files no longer contain sensitive information, you can now include them in source control or upload them to a shared codebase. Exist sure to keep the keystore.backdrop file secure. This may include removing it from your source command system.
Source: https://developer.android.com/studio/publish/app-signing
0 Response to "Android Apk Upload Failed Signed With Different Certificate"
Post a Comment